Originally posted by sandy8925
View Post
Announcement
Collapse
No announcement yet.
Intel Open-Sources New TPM2 Software Stack
Collapse
X
-
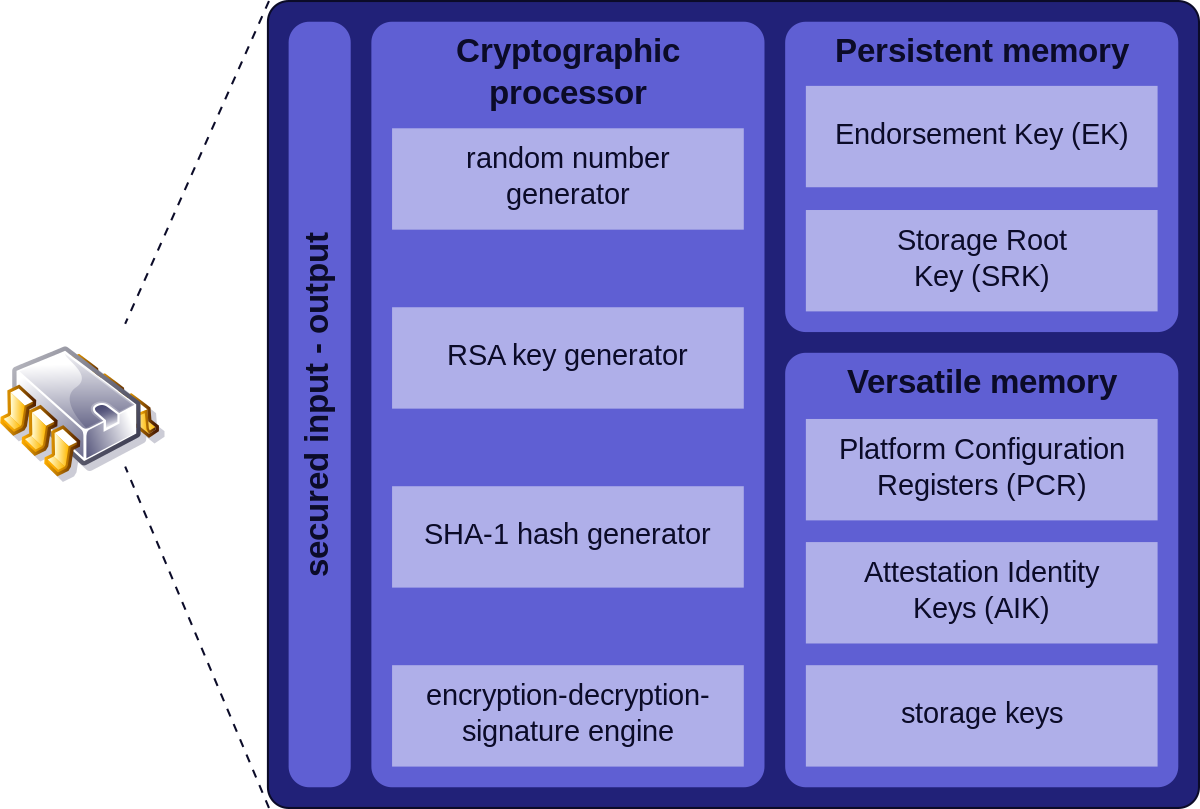
TPM isn't a mini-computer, it's a hardware accelerator for some crypto functions, it has a RNG, and has secure storage for keys. Its bus has no access to a damn.Last edited by starshipeleven; 03 September 2018, 03:43 AM.
-
The TPM spec is open, the drivers are open, it doesn't have access to main memory like Intel ME does AFAICT under any number of it's modes and possible design applications. https://trustedcomputinggroup.org/re...specification/Originally posted by sandy8925 View Post
The problem is that the TPM hardware chip contains closed-source firmware, and is essentially a mini-computer. We don't know what it can access and what it's doing. All we know is that we can securely store and retrieve keys - but no way of knowing if it's actually secure, and whether or not there are backdoors.
It stores numbers securely, and either the BIOS or the OS (face/thumb print recognition etc..) can query these numbers given certain conditions. Secure key storage is a pretty old problem, If Atmel's TPM is insecure or has a backdoor, you can switch to others (giving Atmel enough reason to not do those things). These are basically the same guarantees you have with any peripheral connected to any I/O port on your computer. It's up to you if you want to store certain keys or not in a TPM, but I would say in most circumstances, it can make for an additional layer of security, that's just as importantly practical enough to use for the average user. I think they should be more widespread because of this.
Leave a comment:
-
Originally posted by Slithery View PostDoes anyone know if there are any other hardware providers?
Leave a comment:
-
all hardware inside your computer is closed source and you don't know what it can access and what it's doing. so nothing changedOriginally posted by sandy8925 View PostThe problem is that the TPM hardware chip contains closed-source firmware, and is essentially a mini-computer. We don't know what it can access and what it's doing. All we know is that we can securely store and retrieve keys - but no way of knowing if it's actually secure, and whether or not there are backdoors.
Leave a comment:
-
lol. with full disk encryption your cpu sees all decrypted data because without cpu you can't do anything. encryption is not against your cpu while it is running, it is against stealing drive and putting it in other computerOriginally posted by dwagner View Post"Used for full disk encryption" only by people who earnestly believe that their few-cents-TPM chip could encrypt/decrypt data at the I/O rate of modern NVMe storage. Less misguided people know that the CPU will need to know the symmetric encryption key basically all the time while the system is running, so it isn't any safer when it is also stored in the TPM
- Likes 1
Leave a comment:
-
Trusted by user of course. Intel doesn’t have to trust TPM, they know how it works. But users doesn’t know so they have to trust.Originally posted by tildearrow View PostI feel like asking. When they say "trusted", do they mean "trusted by Intel", or " trusted by the user"? Because if it's the former, then it is a misnomer...
Leave a comment:
-
Then this is about a "secure boot" mechanism, not really about disk encryption. A thieve stealing a notebook steals both the storage device and the TPM that contains the decryption key. Turning the machine on, booting the system installed on it means he is only one DMA access or cold-boot-attack away from the encryption key, which by then resides in ordinary DRAM. Had the encryption key not be stored in the TPM, but to be entered by the legitimate user, such attack would not be feasible.Originally posted by nh2_ View PostI think the idea is that the TPM stores they keys for full-disk encryption, and hands them to the CPU only if trusted software is running.
Leave a comment:

Leave a comment: