Originally posted by dwagner
View Post
Announcement
Collapse
No announcement yet.
Intel Open-Sources New TPM2 Software Stack
Collapse
X
-
all hardware inside your computer is closed source and you don't know what it can access and what it's doing. so nothing changedOriginally posted by sandy8925 View PostThe problem is that the TPM hardware chip contains closed-source firmware, and is essentially a mini-computer. We don't know what it can access and what it's doing. All we know is that we can securely store and retrieve keys - but no way of knowing if it's actually secure, and whether or not there are backdoors.
Comment
-
Originally posted by Slithery View PostDoes anyone know if there are any other hardware providers?
Comment
-
The TPM spec is open, the drivers are open, it doesn't have access to main memory like Intel ME does AFAICT under any number of it's modes and possible design applications. https://trustedcomputinggroup.org/re...specification/Originally posted by sandy8925 View Post
The problem is that the TPM hardware chip contains closed-source firmware, and is essentially a mini-computer. We don't know what it can access and what it's doing. All we know is that we can securely store and retrieve keys - but no way of knowing if it's actually secure, and whether or not there are backdoors.
It stores numbers securely, and either the BIOS or the OS (face/thumb print recognition etc..) can query these numbers given certain conditions. Secure key storage is a pretty old problem, If Atmel's TPM is insecure or has a backdoor, you can switch to others (giving Atmel enough reason to not do those things). These are basically the same guarantees you have with any peripheral connected to any I/O port on your computer. It's up to you if you want to store certain keys or not in a TPM, but I would say in most circumstances, it can make for an additional layer of security, that's just as importantly practical enough to use for the average user. I think they should be more widespread because of this.
Comment
-
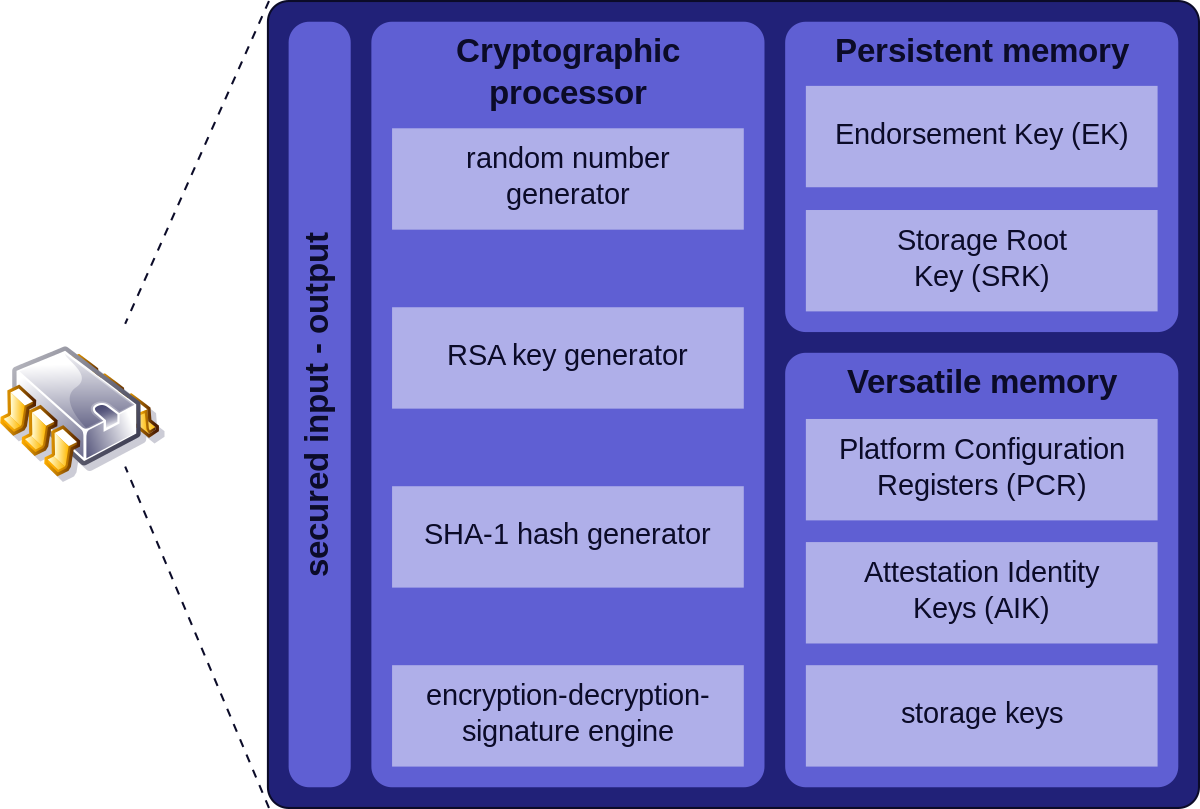
TPM isn't a mini-computer, it's a hardware accelerator for some crypto functions, it has a RNG, and has secure storage for keys. Its bus has no access to a damn.Originally posted by sandy8925 View PostThe problem is that the TPM hardware chip contains closed-source firmware, and is essentially a mini-computer. We don't know what it can access and what it's doing. All we know is that we can securely store and retrieve keys - but no way of knowing if it's actually secure, and whether or not there are backdoors.Last edited by starshipeleven; 03 September 2018, 03:43 AM.
Comment
-
I believe my Acer desktop uses Intel ME for the TPM. tpm.msc under Windows reported the TPM version to be the same version as the ME firmware (11.8.something), and upon using me_cleaner to set the HAP bit (gracefully disable Intel ME), the TPM could not be enabled again nor does the BIOS option reveal any options for it anymore.Originally posted by audir8 View Post
The TPM spec is open, the drivers are open, it doesn't have access to main memory like Intel ME does AFAICT under any number of it's modes and possible design applications. https://trustedcomputinggroup.org/re...specification/
It stores numbers securely, and either the BIOS or the OS (face/thumb print recognition etc..) can query these numbers given certain conditions. Secure key storage is a pretty old problem, If Atmel's TPM is insecure or has a backdoor, you can switch to others (giving Atmel enough reason to not do those things). These are basically the same guarantees you have with any peripheral connected to any I/O port on your computer. It's up to you if you want to store certain keys or not in a TPM, but I would say in most circumstances, it can make for an additional layer of security, that's just as importantly practical enough to use for the average user. I think they should be more widespread because of this.
Comment
-
This is probably true for some OEM manufacturers, but as the me_cleaner README notes, with enough reverse engineering you can get some functionality back, or not lose any functionality after flashing. I've yet to try it on my machines, but I look forward to finding out how ASUS/Lenovo do things when I do.Originally posted by Espionage724 View Post
I believe my Acer desktop uses Intel ME for the TPM. tpm.msc under Windows reported the TPM version to be the same version as the ME firmware (11.8.something), and upon using me_cleaner to set the HAP bit (gracefully disable Intel ME), the TPM could not be enabled again nor does the BIOS option reveal any options for it anymore.
You can also get a TPM with coreboot in libre laptops: https://puri.sm/posts/tpm-addon-for-librem-laptops/
Comment
-
That's a "software TPM". It is the cheapest of the possible TPM systems, and imho the worst one from a security standpoint.Originally posted by Espionage724 View PostI believe my Acer desktop uses Intel ME for the TPM. tpm.msc under Windows reported the TPM version to be the same version as the ME firmware (11.8.something), and upon using me_cleaner to set the HAP bit (gracefully disable Intel ME), the TPM could not be enabled again nor does the BIOS option reveal any options for it anymore.
Comment
-
If the device was using the ME for the TPM provider, you will lose the TPM if you neuter the ME. Because it's the ME that is the TPM in that system, there is no dedicated hardware.Originally posted by audir8 View Post
This is probably true for some OEM manufacturers, but as the me_cleaner README notes, with enough reverse engineering you can get some functionality back, or not lose any functionality after flashing. I've yet to try it on my machines, but I look forward to finding out how ASUS/Lenovo do things when I do.
You can also get a TPM with coreboot in libre laptops: https://puri.sm/posts/tpm-addon-for-librem-laptops/
But anwyay, who cares about TPM.
Comment

Comment