Skype Goes After Reverse-Engineering
In early June I mentioned the Skype protocol was reverse-engineered by a researcher. He was successful in reverse-engineering the Skype 1.4 protocol and subsequently wrote a "send message to Skype" open-source demo program. He followed through and published details regarding the Skype protocol.
A day later I was proactively contacted by a public relations agency representing Skype. The vice president of the PR company was informing me that Skype would be going after this researcher for "unauthorized use of our application for malicious activities" and "We are taking all necessary steps to prevent/defeat nefarious attempts to subvert Skype's experience." It looks like they did.
Only when writing about the new SkypeKit release did this reverse-engineering over the summer come back to mind. When checking out the skype-open-source blog where this work was published, there were multiple DMCA takedowns.
The day of publishing his initial details, Google's Blogger (where his blog is hosted) received a DMCA (Digital Millenium Copyright Act) notice that two of his blog entries had to be removed: the post about his success in reverse-engineering the Skype protocol and then a second post about more technical details.
The complainant issuing the DMCA notice was in fact "Skype Inc" and the basis for the complaint is "Source code. The publication of this code, in addition to infringing Skype's intellectual property rights, may encourage improper spamming activities." (Google publishes DMCA complaints to ChillingEffects.org.)
Skype issued a second DMCA copyright notice after this researcher published more Skype related code. Those files have since moved to being hosted elsewhere. Skype is claiming copyright on the code even though the open-source code was written by the researcher. Another DMCA takedown attempt regarding the same work was issued again in early August when the researcher tried doing a DMCA counter-notice, and he ended up putting up links again to this "copyrighted" work.
The links seem to be up right now for his "Epycs" code and it's since propagated to various file sharing web-sites. It's also hosted on GitHub, but the skypeopensource user has limited activity there beyond hosting files from June and July.
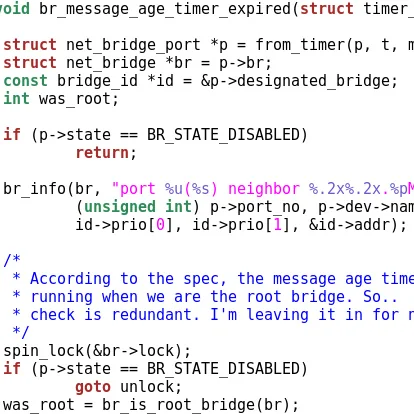
The Epycs code allows sending messages to Skype users by emulating the Skype 1.4 protocol session handshake. Skype Inc ended up abandoning support for this older version of the protocol. According to a status update from the beginning of October, the researcher is working on extensively patching Skype v4.1 and Skype 3.8 for future work. "And then we can continue analyzing and writing a new (updated) protocol for session handshake to send messages to any skype version, including skype v5.x binary." Evidently things have changed quite a bit in the latest Skype client binaries and the protocol itself.
For reference, it does appear that this researcher is not doing "clean-room" reverse engineering. One of the comments he writes on his blog reads, "It is because I have only de-obfuscted 3.8 and 4.1(BETA) versions of skype binary." (In response to why he isn't targeting Skype 5 support at this time.)
It is a Free Software Foundation high priority project to create an open-source alternative to Skype, but so far there hasn't been much concerted effort in this direction.
42 Comments

